Information regarding a critical 0-day vulnerability affecting the VMware Workspace ONE Access and Identity Manager was disclosed and designated CVE-2022-22954 which allows an un-authenticated attacker to execute arbitrary code on vulnerable servers. On April 14th, CISA & US-Cert added CVE-2022-22954 to their catalog of known exploited vulnerabilities after a number of Proof-of-Concept (PoC) exploits were published online and exploit activity was actively observed. Given the impact and severity of the vulnerability, Sn1perSecurity has released an out-of-band update to help detect vulnerable servers in your environment using Sn1per Professional.
Severity: CRITICAL | Exploit Available: Yes | Exploitability: Easy | Remotely Exploitable: Yes
Scanning for VMware Workspace ONE Access freemarker SSTI (CVE-2022-22954)
To detect the CVE-2022-22954 vulnerability using Sn1per Professional, you will need to do the following:
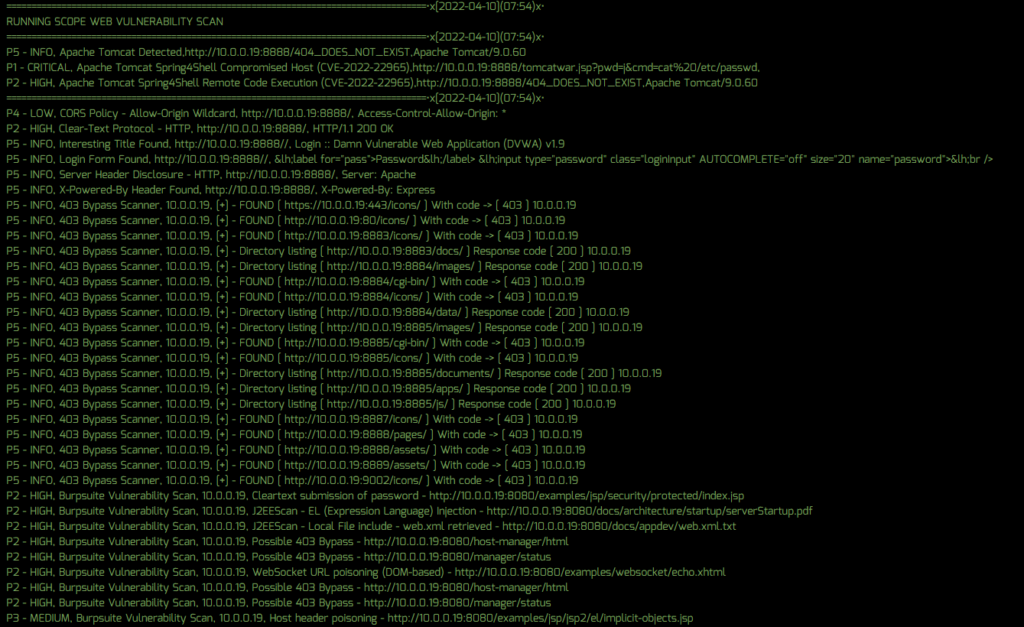
- Apply the template update from the Sn1per Professional “Updates” panel
- Ensure that the “SC0PE_VULNERABLITY_SCANNER” is set to “1” in your Sn1per configuration
- Run a scan of your network using the normal Sn1per scan process
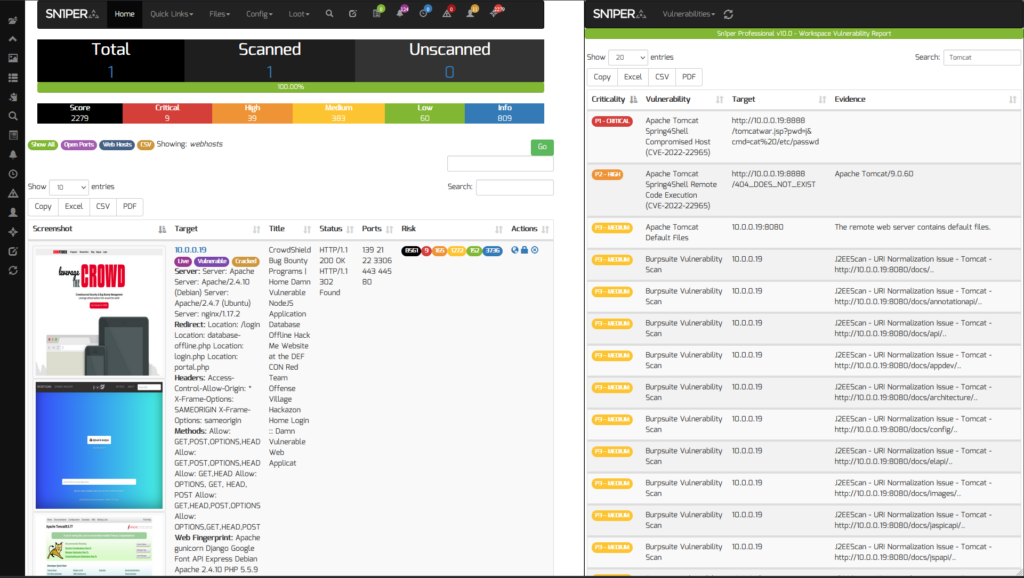
After the scan finishes, you can then view all vulnerable instances from the Sn1per Professional “Vulnerability Report Viewer“.