A critical vulnerability affecting the Atlassian Confluence was disclosed and designated CVE-2022-26134 which allows an un-authenticated attacker to execute arbitrary code on vulnerable servers. A number of Proof-of-Concept (PoC) exploits were published online and exploit activity is actively being observed. Given the impact and severity of the vulnerability, Sn1perSecurity has released an out-of-band update to help detect vulnerable servers in your environment using Sn1per Professional and Sn1per Enterprise.
Severity: CRITICAL | Exploit Available: Yes | Exploitability: Easy | Remotely Exploitable: Yes
Detect CVE-2022-26134 with Sn1per
To detect the CVE-2022-26134 vulnerability using Sn1per, do the following:
- Apply the template update from the Sn1per “Updates” panel.
- Ensure that the “SC0PE_VULNERABLITY_SCANNER” is set to “1” in your Sn1per configuration or choose the default scan profile (ie. /sniper/conf/default) when running the scan.
- For multi-host scans, select “Live Web Hosts” from the “Multi-Host Scan” drop down menu.
- Select the config file set in the step #2.
- Set the number of “Tasks” to run simultaneously. For most environments (3-5 tasks should be sufficient without taxing the network too much).
- Hit the “Scan” button to start the scan.
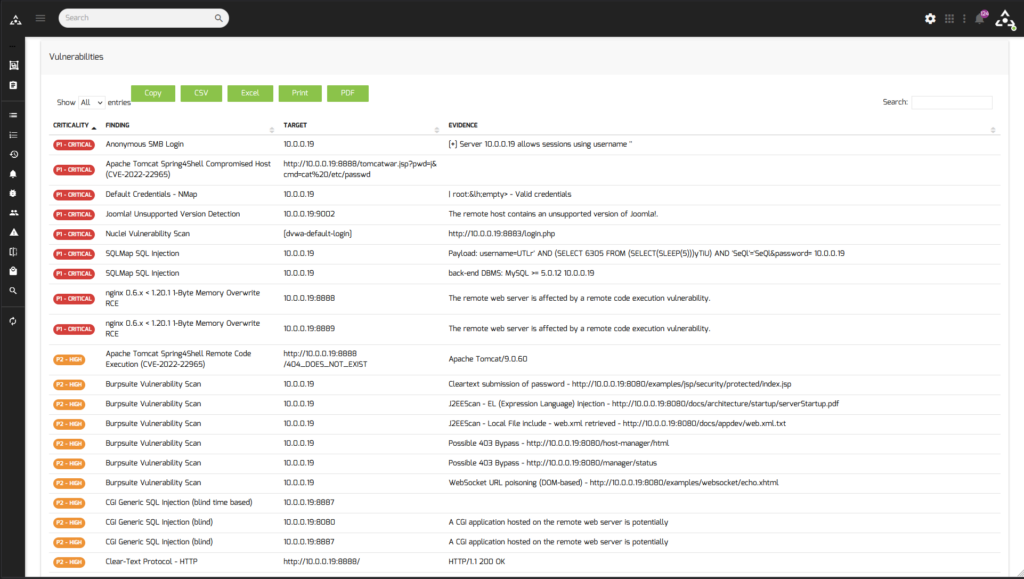
- Use the Sn1per Vulnerability Report Viewer to view all active scan results.
After the scan finishes, you can then view all vulnerable instances from the Sn1per “Vulnerability Report Viewer“.
Remediation
Atlassian recommends that you upgrade to the latest Long Term Support release. For a full description of the latest version, see the Confluence Server and Data Center Release Notes. You can download the latest version from the download centre.
Note: If you run Confluence in a cluster, you will not be able to upgrade to the fixed versions without downtime, also known as a rolling upgrade. Follow the steps in Upgrading Confluence Data Center.
NOTE: This update is only available for Sn1per Professional v10.0 and Sn1per Enterprise customers.