Kali 2021.2 / Ubuntu 20.04.2.0 LTS Support
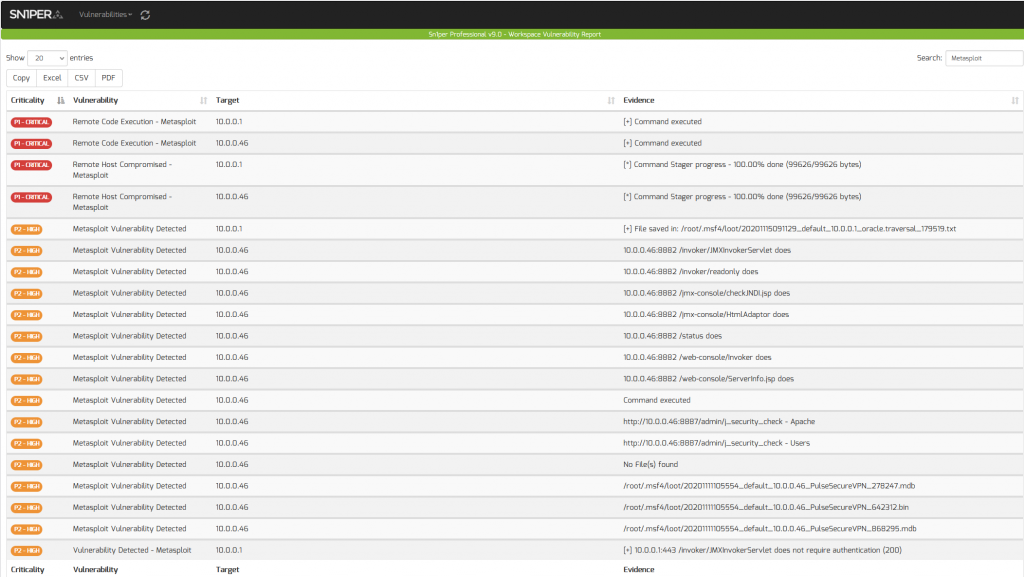
Metasploit Vulnerability & Compromise Detection
Another major improvement in v9.2 is a new sc0pe parser for Metasploit. This will allow customers to automatically import all vulnerabilities detected using Metasploit directly into the Sn1per Professional v9.0 for improved vulnerability analytics and reporting.
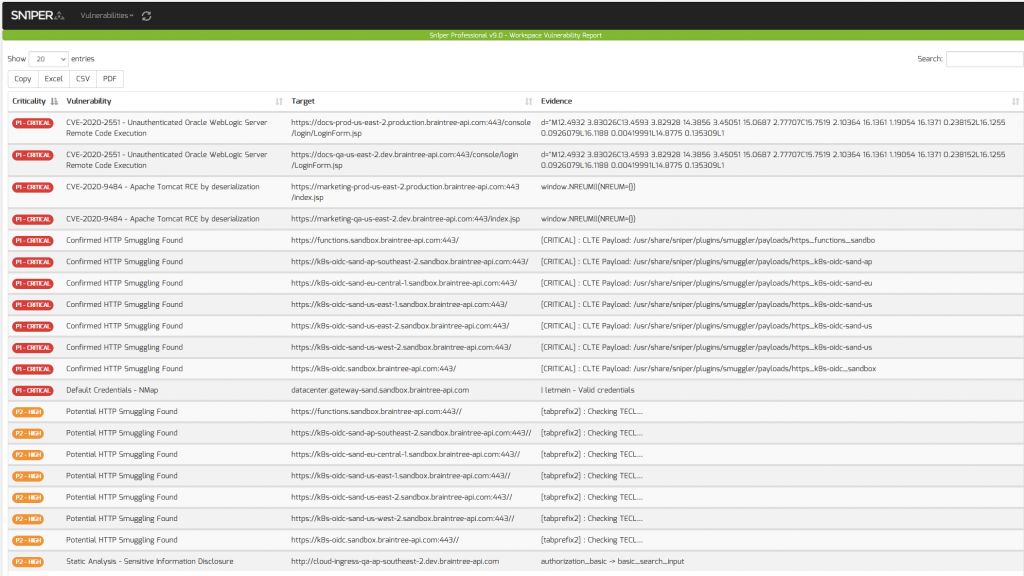
HTTP Smuggling Detection
Starting in Sn1per SE v9.2, we’ve also added automatic scanning and detection for HTTP smuggling which will import all vulnerable instances into the Sn1per Professional v9.0 vulnerability report viewer.
Improved DNS Reconnaissance
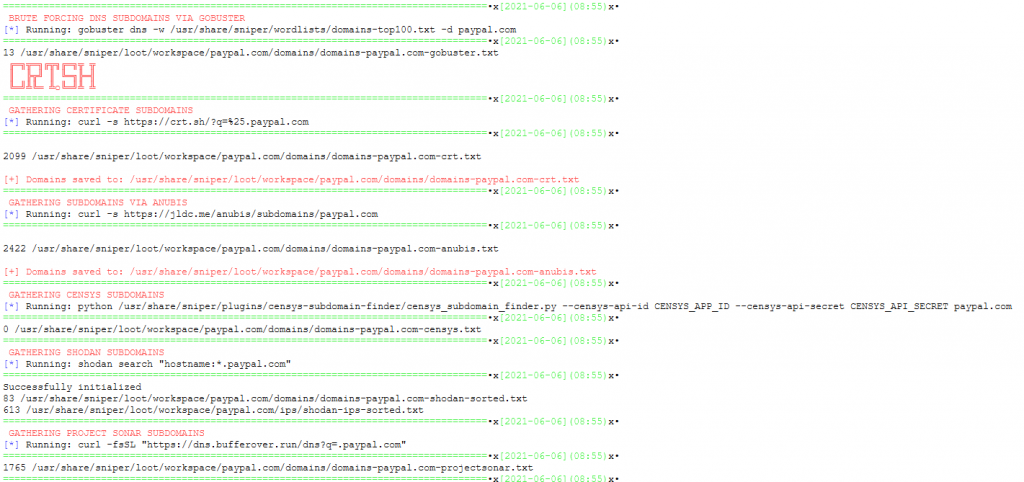
New in v9.2 is the addition of PureDNS which is an improved wrapper around MassDNS, along with an updated DNS resolver list for improved speed, wildcard detection and accuracy when scanning for valid sub-domains.
Resolvable Host Check
In an effort to improve scan efficiency in Sn1per while scanning hundreds or possibly even thousands of discovered sub-domains, we’ve added a new setting (RESOLVABLE_CHECK) to the /root/.sniper.conf to automatically skip any hosts which are not DNS resolvable (ie. no valid DNS record exists). Customers should see a drastic performance increase when running multi-threaded discovery scans against all domains as a result.
Recon & Discover Mode Auto-Scan Options
New settings were added to the Sn1per configuration (/root/.sniper.conf) file to scan all discovered targets automatically when running ‘recon’ or ‘discover’ mode. This will provide greater flexibility and fine tuning while running either scan mode going forward. For instance, when running ‘recon’ mode to discover all sub-domains on a target, you may want to automatically scan all sub-domains discovered. Well, now you can!
NOTE: This setting is disabled by default. To enable, set SCAN_ALL_DISCOVERED_DOMAINS=”1″ in your /root/.sniper.conf file.
##-------------------------------------------------------## DISCOVER & RECON MODE AUTO-SCAN SETTINGS SCAN_ALL_DISCOVERED_DOMAINS="0" SCAN_ALL_DISCOVERED_TASKS="5" SCAN_ALL_DISCOVERED_CONF="$INSTALL_DIR/conf/flyover_mode" SCAN_ALL_DISCOVERED_MODE="normal"
Verbose Settings and Commands
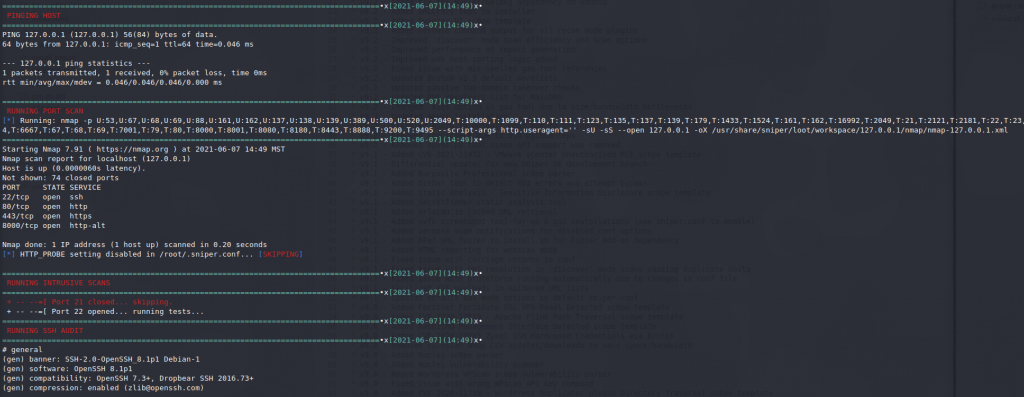
We added verbose output to Sn1per which will show all settings enabled at the beginning of every Sn1per scan as well as any modules which are disabled and skipped to improve visibility and awareness.
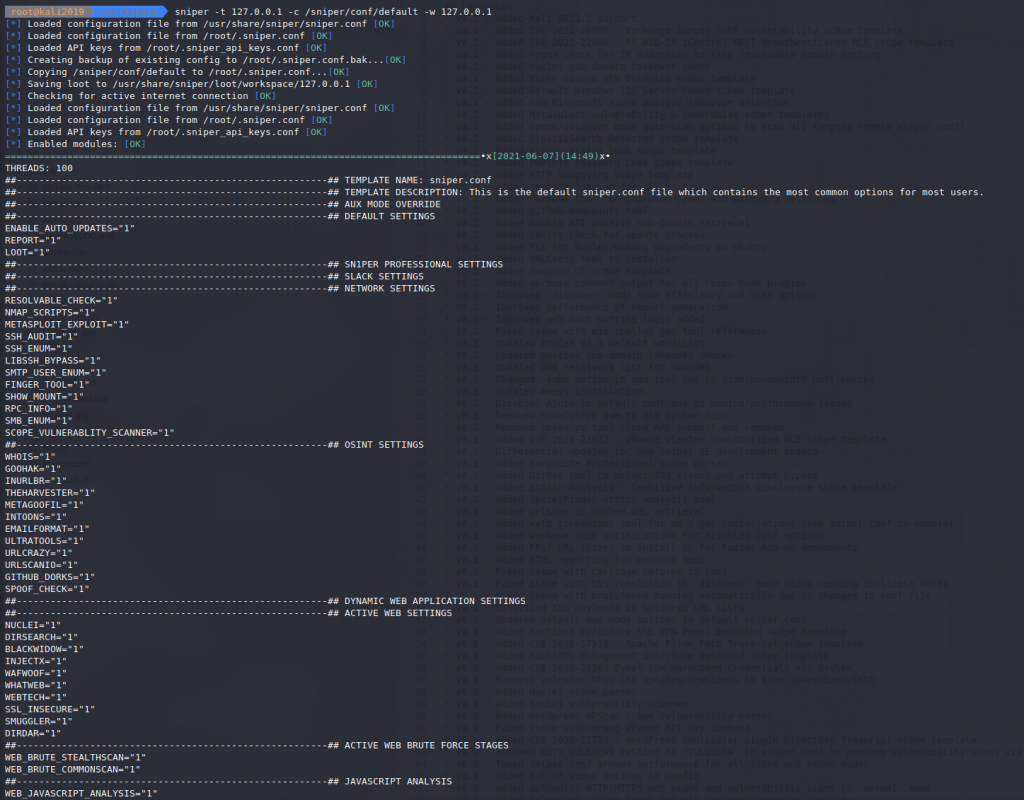
You will also noticed the full command(s) being executed for various key modules (ie. NMap and various other tools) to see exactly what is being executed at run time.
Github Endpoints
Another new tool added in v9.2 is a Github Endpoints script to automatically import all endpoints for a target from Github.
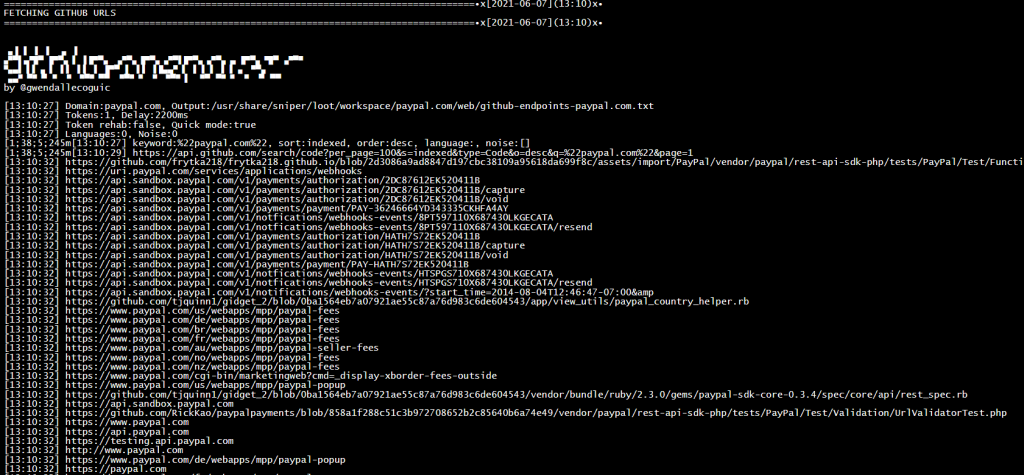
NOTE: To activate, you will need to enable the “GITHUB_ENDPOINTS” setting in /root/.sniper.conf and set the “GITHUB_API_KEY” setting in the /root/.sniper_api_keys file.
Anubis API Added
Anubis API was added as yet another passive recon source to retrieve known sub-domains from a target. This combined with other existing passive and active sources creates a powerful recon workflow to easily and quickly retrieve all sub-domains from a target.
Update Instructions
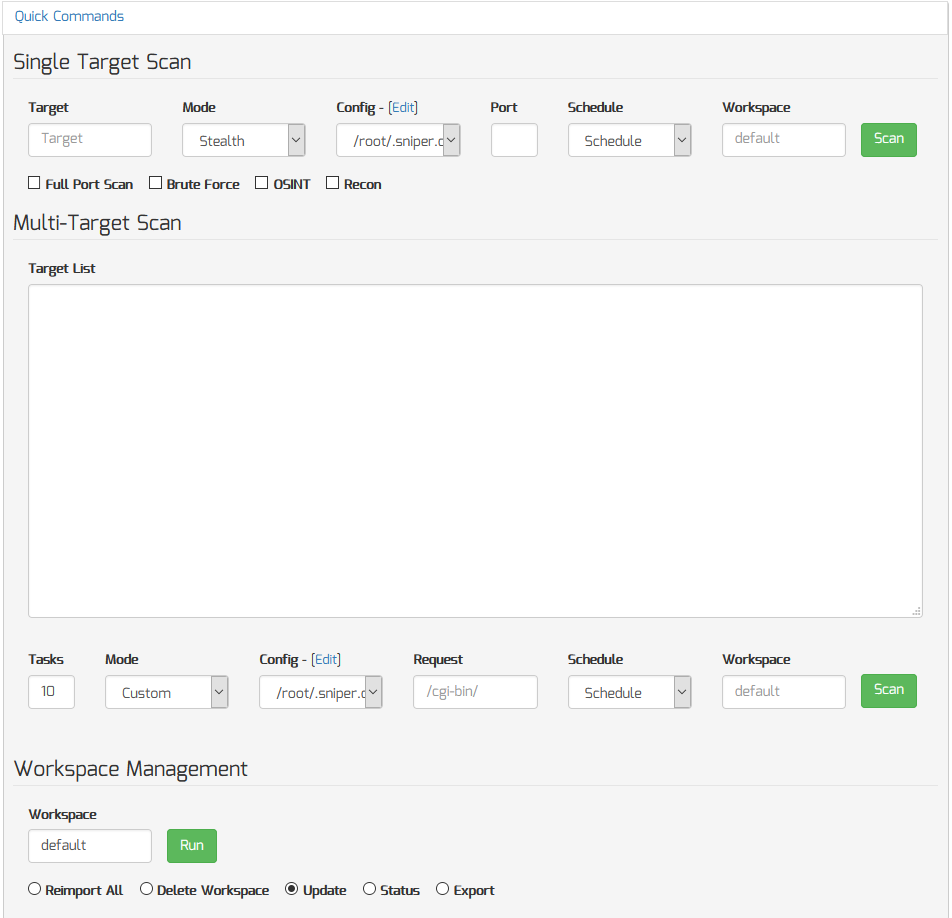
If you’re a current Sn1per Professional v9.0 customer, you have two options to upgrading the v9.2:
- From a ‘root’ terminal, run the ‘sniper -u’ command
- From the Sn1per Professional v9.0 Workspace Navigator, click the “Quick Commands” panel and run the “Update” option
Changelog
This post outlines some of the key features in v9.2. For a full list of changes, see below for more details:
* v9.2 – Added Kali 2021.2 support
* v9.2 – Added CVE-2021-26855 – Exchange Server SSRF Vulnerability sc0pe template
* v9.2 – Added CVE-2021-22986 – F5 BIG-IP iControl REST Unauthenticated RCE sc0pe template
* v9.2 – Added regex check for IP addresses to skip resolvable domain setting
* v9.2 – Added nuclei sub-domain takeover check
* v9.2 – Added Pulse Secure VPN Detected sc0pe template
* v9.2 – Added Default Windows IIS Server Found sc0pe template
* v9.2 – Added new Microsoft Azure passive takeover detection
* v9.2 – Added Metasploit vulnerability & compromise sc0pe templates
* v9.2 – Added recon/discover mode auto-scan options to scan all targets (check sniper.conf)
* v9.2 – Added ElasticSearch Detected sc0pe template
* v9.2 – Added server-status leak sc0pe template
* v9.2 – Added PHPInfo Password Leak sc0pe template
* v9.2 – Added HTTP Smuggling Sc0pe template
* v9.2 – Added verbose logging for all port scans
* v9.2 – Added PureDNS tool for improved speed and wildcard filtering
* v9.2 – Added github-endpoints tool
* v9.2 – Added Anubis API passive sub-domain retrieval
* v9.2 – Added sanity check for update process
* v9.2 – Added fix for Nuclei/Golang dependency on Ubuntu
* v9.2 – Added URLCrazy tool to installer
* v9.2 – Added Swagger UI sc0pe template
* v9.2 – Added verbose command output for all recon mode plugins
* v9.2 – Improved ‘discover’ mode scan efficiency and scan options
* v9.2 – Improved performance of report generation
* v9.2 – Improved web host sorting logic added
* v9.2 – Fixed issue with mis-spelled gau tool references
* v9.2 – Updated BruteX v2.3 default wordlists
* v9.2 – Updated passive sub-domain takeover checks
* v9.2 – Updated DNS resolvers list for MassDNS
* v9.2 – Changed -subs option in gau tool due to size/bandswidth bottlenecks
* v9.2 – Updated Amass installation
* v9.2 – Disabled ASnip in default conf due to haning/performance issues
* v9.2 – Removed spoofcheck due to old python deps
* v9.2 – Removed spyse.py tool since API support was removed